nse6_fnc-8.5 dumps are provided by leads4pass top certification experts to help you pass the Fortinet NSE 6 – FortiNAC 8.5 exam.
They provide PDF and VCE, two of the most popular learning tools, from the leads4pass AZ-104 dumps: https://www.leads4pass.com/nse6_fnc-8-5.html to ensure you pass Fortinet NSE 6 – FortiNAC with ease 8.5 Exam.
Just download the nse6_fnc-8.5 dumps and practice to help you successfully pass the Fortinet NSE 6 – FortiNAC 8.5 exam on your first attempt.
First, read nse6_fnc-8.5 free dumps:
QUESTION 1:
What would happen if a port was placed in both the Forced Registration and the Forced Remediation port groups?
A. Both enforcement groups cannot contain the same port.
B. Only at-risk hosts would be impacted.
C. Only rogue hosts would be impacted.
D. Both types of enforcement would be applied.
QUESTION 2:
What causes a host\’s state to change to “at risk”?
A. The host has been administratively disabled.
B. The logged-on user is not found in the Active Directory.
C. The host has failed an endpoint compliance policy or admin scan.
D. The host is not in the Registered Hosts group.
QUESTION 3:
Which three communication methods are used by the FortiNAC to gather information from, and control, infrastructure devices? (Choose three.)
A. SNMP
B. RADIUS
C. FTP
D. CLI
E. SMTP
QUESTION 4:
When you create a user or host profile; which three criteria can you use? (Choose three.)
A. An applied access policy
B. Administrative group membership
C. Location
D. Host or user group memberships
E. Host or user attributes
QUESTION 5:
With enforcement for network access policies and at-risk hosts enabled, what will happen if a host matches a network access policy and has a state of “at risk”?
A. The host is provisioned based on the network access policy.
B. The host is provisioned based on the default access defined by the point of connection.
C. The host is isolated.
D. The host is administratively disabled.
QUESTION 6:
In which view would you find who made modifications to a Group?
A. The Admin Auditing view
B. The Alarms view
C. The Event Management view
D. The Security Events view
QUESTION 7:
Which system group will force at-risk hosts into the quarantine network, based on point of connection?
A. Forced Quarantine
B. Forced Remediation
C. Forced Isolation
D. Physical Address Filtering
QUESTION 8:
In an isolation VLAN, which three services does FortiNAC supply? (Choose three.)
A. DNS
B. NTP
C. SMTP
D. DHCP
E. Web
QUESTION 9:
During the on-boarding process through the captive portal, why would a host that successfully registered remain stuck in the Registration VLAN? (Choose two.)
A. The wrong agent is installed.
B. Bridging is enabled on the host.
C. There is another unregistered host on the same port.
D. The ports default VLAN is the same as the Registration VLAN.
QUESTION 10:
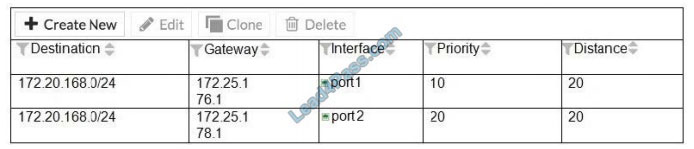
Refer to the exhibit.
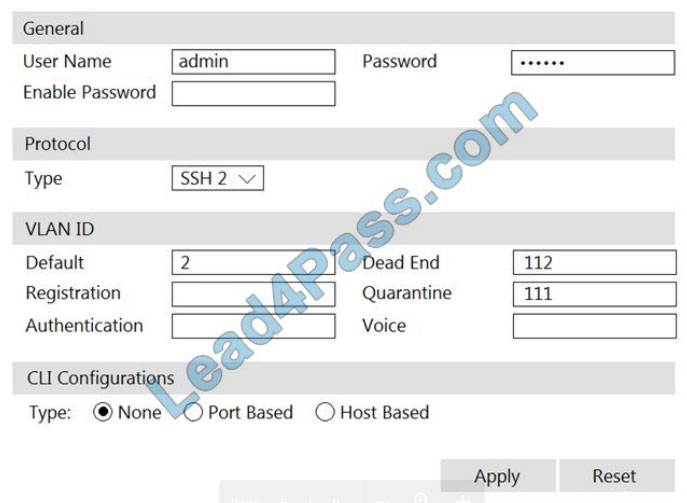
If you are forcing the registration of unknown (rogue) hosts, and an unknown (rogue) host connects to a port on the switch, what will occur?
A. No VLAN change is performed.
B. The host is disabled.
C. The host is moved to VLAN 111.
D. The host is moved to a default isolation VLAN.
QUESTION 11:
Which three circumstances trigger Layer 2 polling of infrastructure devices? (Choose three.)
A. A matched security policy
B. Scheduled poll timings
C. Linkup and Link down traps
D. Manual polling
E. A failed Layer 3 poll
QUESTION 12:
What would occur if both an unknown (rogue) device and a known (trusted) device simultaneously appeared on a port that is a member of the Forced Registration port group?
A. The port would be provisioned to the registration network, and both hosts would be isolated.
B. The port would not be managed, and an event would be generated.
C. The port would be provisioned for the normal state host, and both hosts would have access to that VLAN.
D. The port would be administratively shut down.
QUESTION 13:
How are logical networks assigned to endpoints?
A. Through Layer 3 polling configurations
B. Through network access policies
C. Through FortiGate IPv4 policies
D. Through device profiling rules
……
Verify answer:
| Number | Answers | Explain |
| Q1: | A | |
| Q2: | C | Failure? Indicates that the host has failed the scan. This option can also be set manually. When the status is set to Failure the host is marked”; At Ris”; for the selected scan. |
| Q3: | ABC | Set up SNMP communication with FortiNAC RADIUS Server that is used by FortiNAC to communicate FortiNAC can be configured via CLI to use HTTP or HTTPS for OS updates instead of FTP. |
| Q4: | ACE | |
| Q5: | A | |
| Q6: | A | It\’s important to audit Group Policy changes in order to determine the details of changes made to Group Policies by delegated users. |
| Q7: | B | A remediation plan is established, including forensic analysis and a reload of the system. Also, users are forced to change their passwords as the system held local user accounts. |
| Q8: | ADE | |
| Q9: | AD | Scenario 4: NAT detection disabled, using endpoint compliance policy and agent. |
| Q10: | B | The ability to limit the number of workstations that can connect to specific ports on the switch is managed with Port Security. If these limits are breached, or access from unknown workstations is attempted, the port can do any or all of the following: drop the untrusted data, notify the network administrator, or disable the port. |
| Q11: | BCD | |
| Q12: | C | |
| Q13: | C |
[Google Drive] Download the above nse6_fnc-8.5 free dumps:https://drive.google.com/file/d/1-nluAiCGhIvSDtMjJD5fqD5lcZcMGUBf/
Continue to study 2022 nse6_fnc-8.5 dumps material https://www.leads4pass.com/nse6_fnc-8-5.html, 100% help you pass the Fortinet NSE 6 – FortiNAC 8.5 exam.
Comments are closed.