Good news! New Fortinet NSE4_FGT-7.0 Dumps exam questions, the best solution for NSE 4 Network Security Professional (Fortinet NSE 4 – FortiOS 7.0) exam. Fortinet NSE4_FGT-7.0 exam dumps contain 166 exam questions. We guarantee. NSE4_FGT-7.0 dumps questions are verified. Authentic. The latest NSE4_FGT-7.0 Dumps ensure you are prepared for the Network Security Professional (Fortinet NSE 4 – FortiOS 7.0) exam.
Access the new NSE4_FGT-7.0 dumps below:
Self Check NSE 4 Network Security Professional Certification NSE4_FGT-7.0 Free Dumps
- Which two statements are true about collector agent standard access mode? (Choose two.)
A. Standard mode uses Windows convention-NetBios: Domain\Username.
B. Standard mode security profiles apply to organizational units (OU).
C. Standard mode security profiles apply to user groups.
D. Standard access mode supports nested groups.
Reference: https://docs.fortinet.com/document/fortigate/6.0.0/handbook/482937/agent-based-fsso
2. What is the limitation of using a URL list and application control on the same firewall policy, in NGFW policy-based mode?
A. It limits the scope of application control to the browser-based technology category only.
B. It limits the scope of application control to scan application traffic based on application category only.
C. It limits the scope of application control to scan application traffic using parent signatures only
D. It limits the scope of application control to scan application traffic on DNS protocol only.
3. Which two statements about SSL VPN between two FortiGate devices are true? (Choose two.)
A. The client FortiGate requires a client certificate signed by the CA on the server FortiGate.
B. The client FortiGate requires a manually added route to remote subnets.
C. The client FortiGate uses the SSL VPN tunnel interface type to connect SSL VPN.
D. Server FortiGate requires a CA certificate to verify the client FortiGate certificate.
Reference: https://docs.fortinet.com/document/fortigate/6.2.9/cookbook/266506/ssl-vpn-with-certificateauthentication
4. Which statement about video filtering on FortiGate is true?
A. Full SSL Inspection is not required.
B. It is available only on a proxy-based firewall policy.
C. It inspects video files hosted on file-sharing services.
D. Video filtering FortiGuard categories are based on web filter FortiGuard categories.
Reference: https://docs.fortinet.com/document/fortigate/7.0.0/new-features/190873/video-filtering
5. Why does FortiGate keep TCP sessions in the session table for some seconds even after both sides (client and server) have terminated the session?
A. To remove the NAT operation.
B. To generate logs
C. To finish any inspection operations.
D. To allow for out-of-order packets that could arrive after the FIN/ACK packets.
6. When a firewall policy is created, which attribute is added to the policy to support recording logs to a FortiAnalyzer or a FortiManager and improves functionality when a FortiGate is integrated with these devices?
A. Log ID
B. Universally Unique Identifier
C. Policy ID
D. Sequence ID
Reference: https://docs.fortinet.com/document/fortigate/6.0.0/handbook/554066/firewall-policies
7. Which two types of traffic are managed only by the management VDOM? (Choose two.)
A. FortiGuard web filter queries
B. PKI
C. Traffic shaping
D. DNS
8. Which three criteria can a FortiGate use to look for a matching firewall policy to process traffic? (Choose three.)
A. Source is defined as Internet Services in the firewall policy.
B. Destination is defined as Internet Services in the firewall policy.
C. Highest to lowest priority defined in the firewall policy.
D. Services defined in the firewall policy.
E. Lowest to the highest policy ID number.
Reference: https://kb.fortinet.com/kb/documentLink.do?externalID=FD47435
9. Refer to the exhibit.
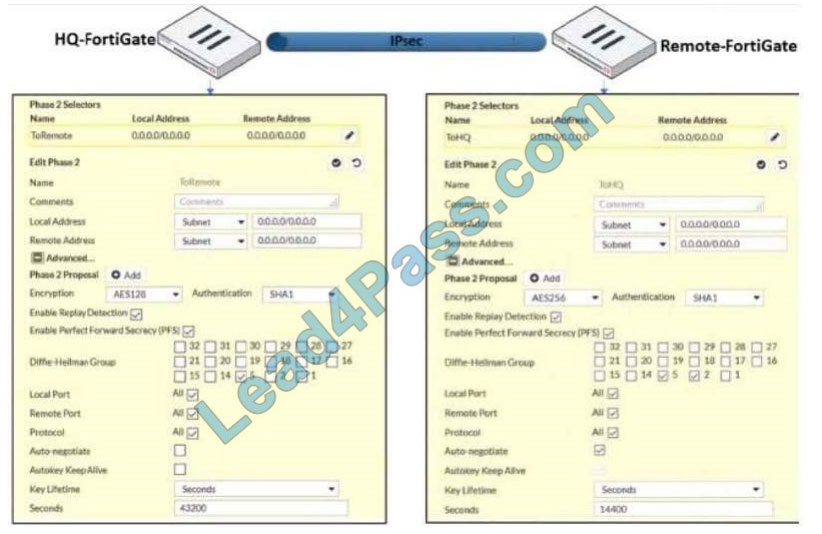
A network administrator is troubleshooting an IPsec tunnel between two FortiGate devices. The administrator has determined that phase 1 status is up. but phase 2 fails to come up. Based on the phase 2 configuration shown in the exhibit, what configuration change will bring phase 2 up?
A. On HQ-FortiGate, enable Auto-negotiate.
B. On Remote-FortiGate set Seconds to 43200.
C. On HQ-FortiGate, enable Diffie-Hellman Group 2.
D. On HQ-FortiGate set Encryption to AES256.
Reference: https://docs.fortinet.com/document/fortigate/5.4.0/cookbook/168495
10. An administrator does not want to report the logon events of service accounts to FortiGate. What setting on the collector agent is required to achieve this?
A. Add the support of NTLM authentication.
B. Add user accounts to Active Directory (AD).
C. Add user accounts to the FortiGate group fitter.
D. Add user accounts to the Ignore User List.
11. Consider the topology: Application on a Windows machine FGT–> Telnet to Linux server. An administrator is investigating a problem where an application establishes a Telnet session to a Linux server over the SSL VPN through FortiGate and the idle session times out after about 90 minutes. The administrator would like to increase or disable this timeout. The administrator has already verified that the issue is not caused by the application or Linux server. This issue does not happen when the application establishes a Telnet connection to the Linux server directly on the LAN. What two changes can the administrator make to resolve the issue without affecting services running through FortiGate? (Choose two.)
A. Set the maximum session TTL value for the TELNET service object.
B. Set the session TTL on the SSLVPN policy to maximum, so the idle session timeout will not happen after 90 minutes.
C. Create a new service object for TELNET and set the maximum session TTL.
D. Create a new firewall policy and place it above the existing SSLVPN policy for the SSL VPN traffic, and set the new TELNET service object in the policy.
12. In an explicit proxy setup, where is the authentication method and database configured?
A. Proxy Policy
B. Authentication Rule
C. Firewall Policy
D. Authentication scheme
Validation results:
| Q1 | Q2 | Q3 | Q4 | Q5 | Q6 | Q7 | Q8 | Q9 | Q10 | Q11 | Q12 |
| BC | B | CD | B | D | B | AC | ABD | C | C | BC | D |
NSE4_FGT-7.0 contains questions and answers, Fortinet NSE4_FGT-7.0 Free PDF Online Download: https://drive.google.com/file/d/1GaV6MWTPlU5eLogXQthNomO856NjNgcJ/view?usp=sharing
New NSE4_FGT-7.0 dumps https://www.leads4pass.com/nse4_fgt-7-0.html. Best Solutions for NSE 4 Cybersecurity Professional (Fortinet NSE 4 – FortiOS 7.0) Exam.

Comments are closed.